Top 7 Cybersecurity Providers for Food & Beverage Manufacturing Companies in California

Food and beverage manufacturers in California need cybersecurity providers that understand operational technology, ransomware risk, and production uptime. The strongest partners combine OT security, executive level leadership, and California-based support. This guide compares seven cybersecurity providers based on OT capability, implementation depth, and manufacturing alignment.
Why Cybersecurity Is Different for Food & Beverage Manufacturers
Food manufacturing cybersecurity protects more than data.
It protects:
- Production continuity
- Refrigeration and cold-chain systems
- PLC and SCADA environments
- Inventory and ERP systems
- Supply chain coordination
OT security in food manufacturing must preserve uptime. Security that disrupts production fails the business.
Quick Comparison Table
Consilien
Southern California

Consilien provides cybersecurity and managed security services to small and mid-market manufacturers across California, including food and beverage operations with uptime-sensitive production environments.
Services and Expertise
- Managed detection and response
- OT-aware IT/OT segmentation
- vCISO leadership
- Incident response planning
- Ransomware containment strategy
- Compliance alignment
- Cloud and ERP security integration
Strengths
- Manufacturing experience
- Executive-level security ownership
- Focus on operational continuity
- Southern California engineering presence
- Integrates enterprise security tools into plant environments
Weaknesses
- Not a standalone ICS product vendor
- Focused primarily on SMB and mid-market firms
Best For
Small and mid-market California food manufacturers needing integrated IT/OT cybersecurity leadership and ongoing management.
Poor Fit
Global enterprises seeking only industrial security software licensing.
Trust and Reputation
Established California presence with experience supporting regulated and manufacturing-driven organizations.
Bottom Line
A California cybersecurity partner focused on securing production environments while preserving uptime.
Dragos
Dragos specializes in industrial control system cybersecurity and OT threat intelligence.
Services and Expertise
- ICS threat intelligence
- OT incident response
- Industrial risk assessments
- Manufacturing-specific research
Strengths
- Deep ICS specialization
- Industrial-focused threat intelligence
- Recognized OT security authority
Weaknesses
- Platform-centric approach
- Designed primarily for large industrial enterprises
Best For
Large food production facilities with complex OT infrastructure.
Poor Fit
Smaller mid-market plants without dedicated OT teams.
Trust and Reputation
Widely recognized in industrial cybersecurity research and OT protection.
Bottom Line
An industrial cybersecurity leader for enterprise OT environments.
Claroty
Claroty focuses on cyber-physical systems protection and OT visibility for industrial environments.
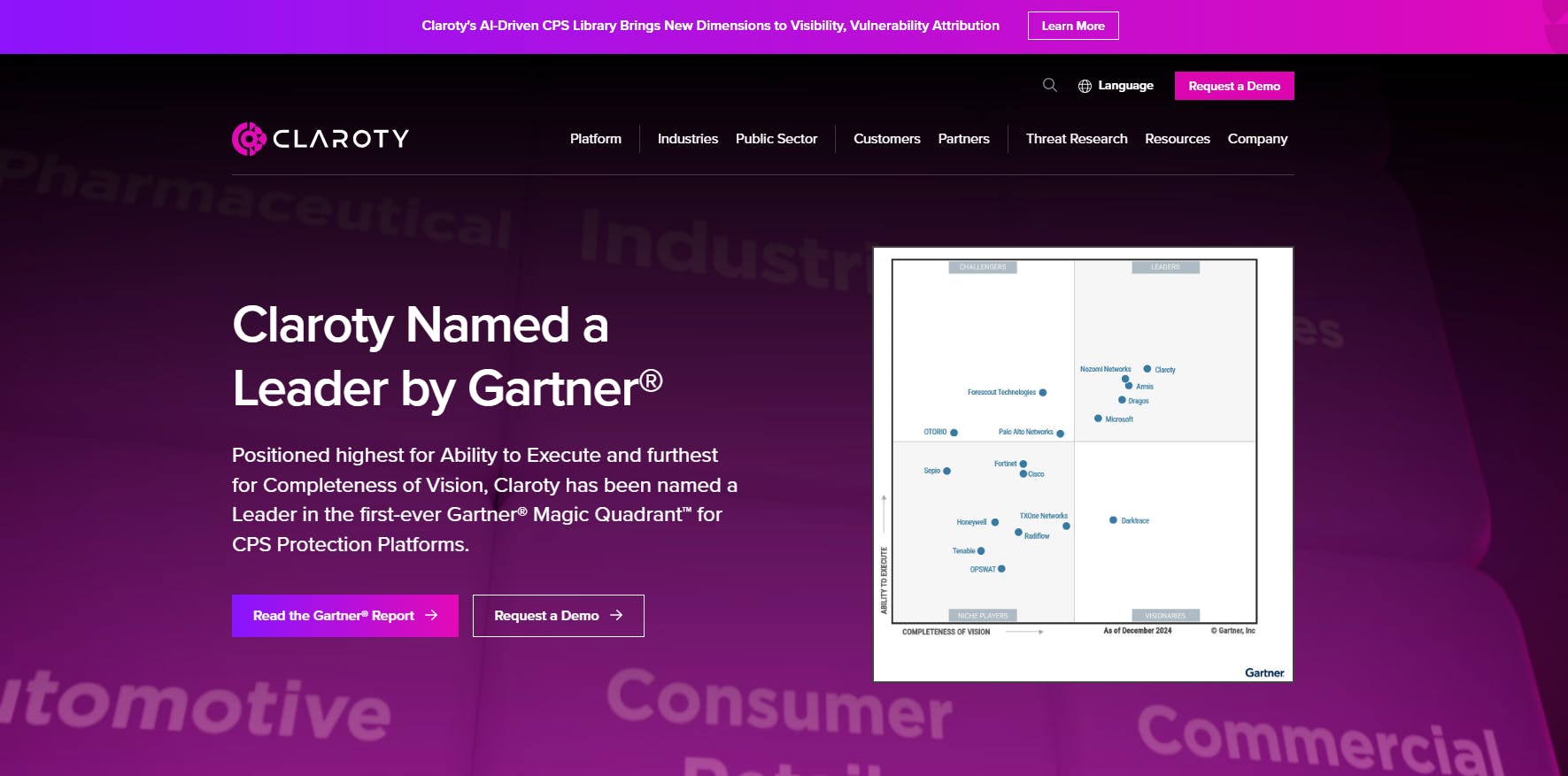
Services and Expertise
- OT asset discovery
- CPS threat detection
- Industrial network monitoring
- Risk assessment tools
Strengths
- Advanced OT visibility
- Strong segmentation capabilities
- Manufacturing-oriented platform
Weaknesses
- Product-driven model
- Implementation often partner-dependent
Best For
OT-heavy food manufacturing facilities requiring industrial visibility.
Poor Fit
Organizations seeking managed operational cybersecurity partnership.
Trust and Reputation
Recognized provider in cyber-physical system protection and OT monitoring.
Bottom Line
A strong OT visibility platform provider for industrial environments.
Palo Alto Networks
Palo Alto Networks is a California-based enterprise cybersecurity provider headquartered in Santa Clara.
Services and Expertise
- Next-generation firewalls
- Cloud security
- Advanced threat detection
- Network segmentation
Strengths
- Enterprise-grade security ecosystem
- Advanced threat prevention
- Broad adoption across industries
Weaknesses
- Enterprise-focused pricing
- Requires integration partners for manufacturing deployment
Best For
Enterprise-scale food manufacturers with hybrid IT environments.
Poor Fit
Smaller manufacturers needing local managed support.
Trust and Reputation
Globally recognized cybersecurity provider headquartered in California.
Bottom Line
An enterprise security leader requiring strong implementation support.
Fortinet
Fortinet provides network-centric cybersecurity solutions from its Sunnyvale headquarters.
Services and Expertise
- Firewall security
- Network segmentation
- Secure SD-WAN
- OT security integrations
Strengths
- Strong secure networking capabilities
- Manufacturing-friendly segmentation
- Broad ecosystem compatibility
Weaknesses
- Product-centric approach
- OT specialization depends on deployment partner
Best For
Network-heavy production environments.
Poor Fit
Facilities seeking fully managed operational cybersecurity leadership.
Trust and Reputation
Widely deployed across enterprise and industrial networks globally.
Bottom Line
A strong infrastructure security provider when properly integrated.
Armis
Armis focuses on asset visibility across IT, IoT, and OT systems.
Services and Expertise
- Device discovery
- Risk mapping
- IoT and OT monitoring
- Exposure management
Strengths
- Strong asset visibility
- IoT and OT discovery capabilities
- Risk prioritization insights
Weaknesses
- Monitoring-focused platform
- Requires broader security architecture integration
Best For
Facilities needing improved visibility into connected devices.
Poor Fit
Organizations requiring full-service cybersecurity management.
Trust and Reputation
Recognized for asset visibility and IoT security capabilities.
Bottom Line
A visibility-focused platform for mixed IT/OT environments.
Nozomi Networks
Nozomi Networks specializes in OT monitoring and industrial anomaly detection.
Services and Expertise
- ICS network monitoring
- Industrial anomaly detection
- OT risk assessment
- Threat intelligence
Strengths
- Deep OT monitoring focus
- Industrial anomaly detection
- Production-level threat visibility
Weaknesses
- Monitoring-first approach
- Requires integration into broader security program
Best For
Industrial operations with high OT complexity.
Poor Fit
Organizations seeking full-service cybersecurity leadership.
Trust and Reputation
Recognized provider in industrial monitoring and ICS security.
Bottom Line
A focused OT monitoring provider for complex industrial environments.
How to Choose the Right Cybersecurity Provider
Food and beverage manufacturers in California should prioritize:
- IT/OT segmentation strategy
- Continuous OT monitoring
- Ransomware containment readiness
- Executive security ownership
- California operational presence
Technology alone doesn’t protect production.
Operational integration does.
Final Guidance
Industrial cybersecurity vendors provide powerful platforms. But food manufacturers need implementation discipline, executive oversight, and uptime-first integration.
Cybersecurity must protect production continuity first.
